When debugging authentication or API issues, inspecting a JSON Web Token (JWT) is often the first step. You need to see exactly what claims the server issued, when the token expires, and whether the payload matches your expectations.
But pasting real authentication tokens into random browser tabs carries significant security risks. This guide explains how to inspect JWT contents safely using a demo token, what the common claims mean, and what you should never paste into an online decoder.
Quick Safety Rule
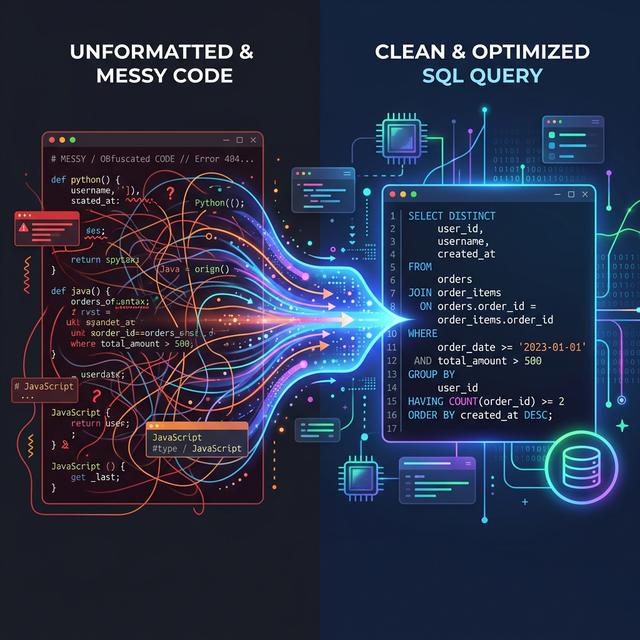
Never paste a production JWT—especially one containing real user data, admin roles, or sensitive secrets—into an online decoder unless you are absolutely certain the tool runs entirely client-side.
If a tool sends your token to a backend server, that token could be logged, intercepted, or abused before it expires. WebToolsPlanet's JWT Decoder runs entirely in your browser, but as a best practice, always generate a safe test token for online debugging.
Example JWT Token
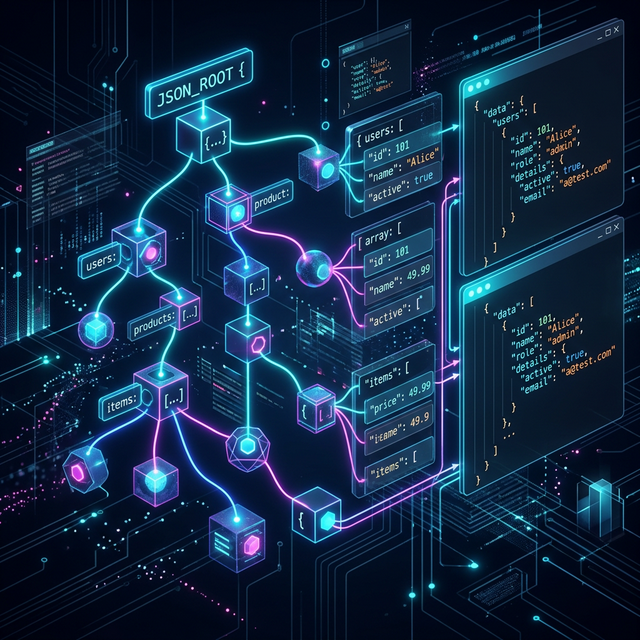
A standard JWT consists of three parts separated by dots: the Header, the Payload, and the Signature. They are Base64Url encoded, which is why they look like a random string of characters.
Here is a safe, dummy JWT you can use to test decoders:
- eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiIxMjM0NTY3ODkwIiwibmFtZSI6IkpvaG4gRG9lIiwiYWRtaW4iOnRydWUsImlhdCI6MTUxNjIzOTAyMiwiZXhwIjoxNTE2MjQyNjIyfQ.SflKxwRJSMeKKF2QT4fwpMeJf36POk6yJV_adQssw5c
Decode the JWT with WebToolsPlanet
When you paste the demo token into the JWT Decoder, it instantly splits and decodes the Base64Url segments into readable JSON format.
The Header will show {"alg": "HS256", "typ": "JWT"}, confirming the algorithm used for the signature. The Payload will reveal the actual claims, such as the user ID, name, admin status, and timestamps.
What Claims Should You Check?
The payload contains "claims," which are statements about the user and additional metadata. When debugging, you usually want to check a few standard registered claims:
- exp (Expiration Time): Is the token already expired? This is a common cause of 401 Unauthorized errors.
- iat (Issued At): When was the token created? Useful for checking if the token is newer than a recent permission change.
- iss (Issuer): Who created and signed this token?
- aud (Audience): Who is this token intended for?
- sub (Subject): The unique identifier for the user (often a user ID).
- Roles or Scopes: Custom claims (like "admin": true) that determine what the user is allowed to do.
What Not to Paste Into an Online Decoder
Because a JWT is just encoded—not encrypted—anyone with the token can read the payload. The signature only prevents tampering, it does not hide the data.
For this reason, you should never paste tokens containing Personally Identifiable Information (PII), customer payment data, active administrative session tokens, or private signing keys into untrusted online tools.
FAQ
Here are some common questions developers have about JWT safety:
- Is it safe to decode a JWT online? Yes, if the tool runs strictly client-side (like WebToolsPlanet) or if you use a safe demo token.
- Can a JWT decoder verify the signature? Some can if you provide the secret key, but you should never paste your server's private signing key into a browser tool.
- What does the payload show? It shows the decoded JSON claims embedded in the token.
- What does exp mean in JWT? It stands for "Expiration Time", defined as a Unix timestamp.
- Should I paste production tokens into online tools? No. Always try to debug using local tools or mock test tokens when dealing with production environments.
Khushbu
Full-Stack Developer & Founder
I build tools I wish existed — fast, free, and private. Every tool runs in your browser because I believe your data should stay yours.
Tools mentioned in this guide